Understanding Supply Chain Attacks: A Growing Threat in Cybersecurity
A supply chain attack is a cybersecurity threat that exploits vulnerabilities within a software’s supply chain. Instead of directly targeting the software itself, attackers focus on less-protected areas, such as software providers, third-party vendors, or service providers. By compromising a single entity within the supply chain, attackers can breach multiple organisations that rely on the same software, causing widespread damage. Embedded systems, including IoT devices, are particularly vulnerable due to their reliance on third-party firmware. These are often minimal with limited security and limited update mechanisms.
The Growing Importance of Supply Chain Security
As organisations increasingly depend on third-party software, cloud services, and external vendors, the attack surface has expanded. Traditional cybersecurity measures often overlook these indirect entry points, making supply chain attacks a favoured strategy for cybercriminals and state-sponsored threat actors. Assessing the security practices of third-party vendors can also be very difficult (often impossible), creating a heavy reliance on trust and making it difficult to produce a valid risk assessment. High-profile incidents, such as the SolarWinds breach (2020) and the Kaseya ransomware attack (2021), have demonstrated how devastating these attacks can be.
For embedded devices, the risks are even greater. Many of these devices run proprietary firmware sourced from multiple vendors, making it difficult to verify the integrity of the entire software stack. Their widespread deployment in infrastructure and across the supply chain makes them a prime target for cyber criminals.
How Supply Chain Attacks Work
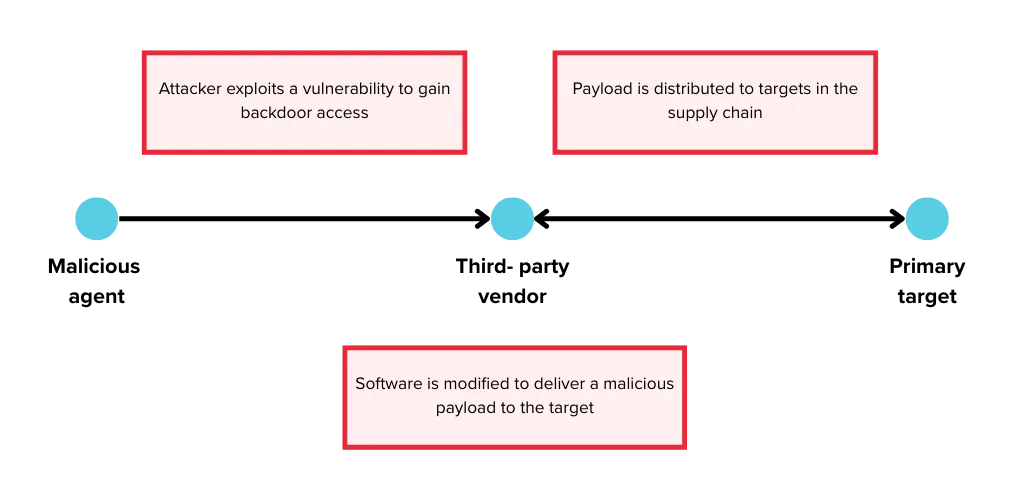
- Gaining Access to the Supplier’s Network – Attackers infiltrate a supplier’s network by targeting weak security protocols, exploiting vulnerable server infrastructure, or leveraging unsafe coding practices.
- Injecting Malicious Code – Once inside, attackers alter the source code or inject malware into software builds and update processes.
- Propagation to End Users – The compromised software is released by the supplier, unaware of the malicious code.
- Execution of the Attack – When customers or users install or update the software, the embedded malware is activated, leading to breaches that may include phishing, malware distribution, data exfiltration, denial-of-service attacks, and botnet deployment.
Notable Examples of Supply Chain Attacks
- SolarWinds Attack (2020)
Beginning in September 2019, hackers compromised SolarWinds’ Orion software by embedding malware into updates that were distributed over several months to approximately 18,000 customers, including U.S. government agencies and private enterprises. This breach opened a back door, allowing the attackers to gain access to sensitive data from major corporations and government agencies, including FireEye, Microsoft, Intel, Cisco, and Deloitte. This attack underscores the importance of a proactive approach to identifying security vulnerabilities and the need for companies to assess the security of third-party software vendors to mitigate risk. - Polyfill CDN Attack (2024)
After being acquired by a Chinese company, Polyfill, a previously open-source CDN focused primarily on providing libraries that support older browsers, was caught injecting malware into websites that embedded its scripts. The malware was quite sophisticated, only activating on mobile devices at specific times and delaying execution when analytics services were detected, thereby remaining undetected itself. The payload was used to redirect users to malicious spam sites, including typo-squatted domains mimicking Google Analytics. One of the reasons this type of attack is so effective is that many users may not even be aware that they were using the vulnerable code. In the case of Polyfill, the library was used as a dependency on many websites and may have been difficult to spot. This incident underscores the importance of rigorous vetting of third-party services and continuous monitoring to prevent unmaintained/vulnerable third-party software from compromising the system. Maintaining a bill of materials (BOM) and monitoring for reported vulnerabilities is a good start. You can find out more about CVE monitoring and software BOM here. - Dragonfly Attack on Energy Sector (2014)
In 2014, the Dragonfly cyber espionage group targeted energy companies across Europe and North America by compromising Industrial Control System (ICS) and Supervisory Control and Data Acquisition (SCADA) software. The attackers injected malware into legitimate software downloads, effectively turning them into a Trojan. Once installed, the malware operated silently in the background, allowing hackers to gain access to ICS networks. This access allowed them to exfiltrate critical data on ICS devices, potentially enabling sabotage or disruption of essential energy infrastructure. This example illustrates the risk of using third-party software, as their security practices may not be transparent, and users have no way of knowing about potential software vulnerabilities they may contain.
Types of Supply Chain Attacks
Supply chain attacks take many forms and aren’t limited to a set of categories or types. It is helpful to know some of the different forms they take, as attackers can target different supply chains depending on their purposes and the type of users they are targeting.
- Third-party software vendors – Attackers compromise trusted software providers to distribute malicious updates to users (e.g. SolarWinds). This method can reach a broad set of targets and relies on the trust users have for reputable software vendors.
- Website Builders & CDNs – Malicious code is injected into website-building services or third-party script libraries, such as Polyfill. Attackers exploit these platforms to compromise multiple websites simultaneously, enabling them to reach a large number of users without directly breaching individual sites. Websites often use old, deprecated libraries that contain vulnerabilities.
- Third-Party Data Stores – Attackers target large data aggregators to steal sensitive information. These attacks appeal to cybercriminals looking to exfiltrate financial, customer, or corporate data that can be sold, ransomed, or used for further attacks. For example, in 2020, Blackbaud, a major provider of fundraising and donor management software, was hacked, resulting in the compromise of sensitive customer data. Blackbaud was forced to pay a ransom.
- Watering Hole Attacks – Attackers target a site or resource that is frequently used by the primary target, identifying weaknesses in the target’s security and manipulating the watering hole to deliver a payload to exploit these weaknesses. The malicious actors exploit the primary target’s trust in the watering hole site.
- Hardware and Firmware Implants – Attackers introduce malicious components at the hardware level. For example, a vulnerable I2C or SPI peripheral in an industrial controller could allow attackers to inject malicious commands at the hardware level, bypassing OS security measures. Malicious firmware could also be installed, as devices often rely on proprietary firmware that cannot be easily audited for backdoors. This is a particular risk with embedded devices that are deployed into sensitive infrastructure.
Preventing Supply Chain Attacks
The use of third-party software significantly increases the number of potential vulnerabilities and, therefore, the attack surface. These vulnerabilities are also more complex to identify and address due to limited access to the third-party software provider’s code. Here are some security principles that will reduce the attack surface as much as possible.
- Zero Trust Principle – Restrict access based on strict authentication and continuous monitoring. The principle of least privilege should be enforced to limit vendor and user access to only essential resources, reducing potential attack surfaces.
- Third-Party Risk Management – Conduct thorough cybersecurity risk assessments before partnering with vendors. Third-party security practices should be audited and monitored to ensure they have taken the necessary steps to minimise their attack surface and address vulnerabilities in their software.
- Timely Patching and Automated Updates – Vendors must apply security patches promptly to minimise attack windows. Automating patching can help prevent delays in vulnerability mitigation. Maintaining an inventory of software dependencies is crucial for effectively tracking security updates and ensuring that all components remain secure.
- AI-Based Threat Detection – As seen in the Polyfill example above, malware is becoming increasingly sophisticated. Technologies like polymorphic malware are making it harder for traditional threat detection algorithms to spot malware. AI-driven detection mechanisms analyse behavioural patterns to identify novel threats before they cause a breach. They may become part of an effective strategy for combating supply chain attacks in the future.
- Employee and Vendor Cybersecurity Training – Automated patching ensures that the latest patches are applied as soon as they are released, thereby removing third-party software vulnerabilities and reducing the attack surface.
Conclusion
Supply chain attacks are an evolving threat that requires a proactive approach to cybersecurity. For embedded systems, the risks are heightened due to long lifecycles, reliance on third-party firmware, and difficulty in patching vulnerabilities post-deployment. Organisations must reassess their security postures, implement stringent vendor management practices, and adopt emerging technologies, such as AI-driven threat detection. By reinforcing principles such as least privilege access, continuous monitoring, secure boot, and firmware validation, businesses can reduce their vulnerability to or participation in these large-scale attacks.
Consult Red has over 20 years of experience working with complex software stacks consisting of a range of vendor and third-party code, at all levels, from chip to cloud. Our security experts can support you in assessing the risks posed by your use of third-party software and services and effectively mitigating these.




